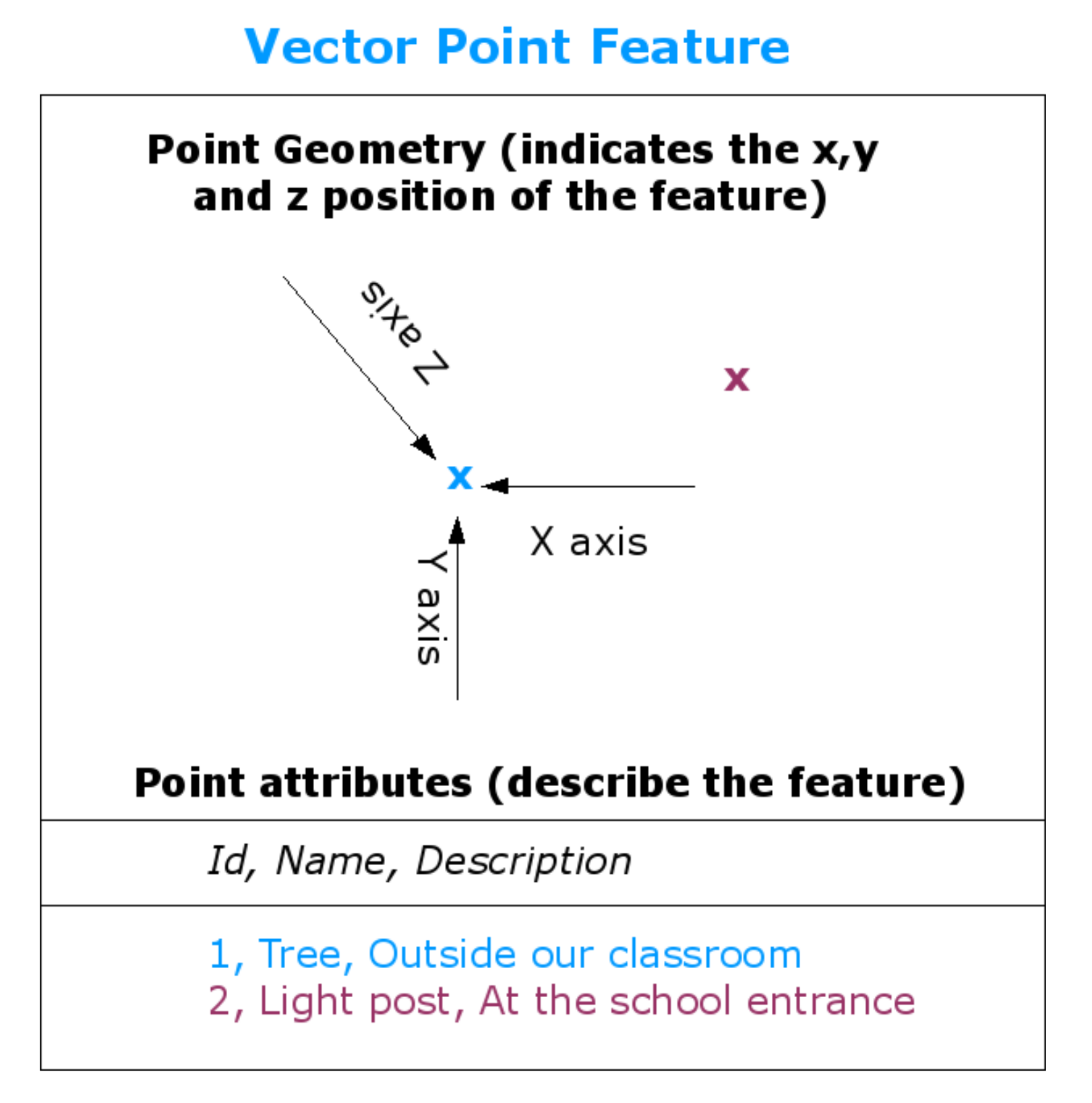
IJGI | Free Full-Text | Development of a 3D WebGIS Application for the Visualization of Seismic Risk on Infrastructural Work
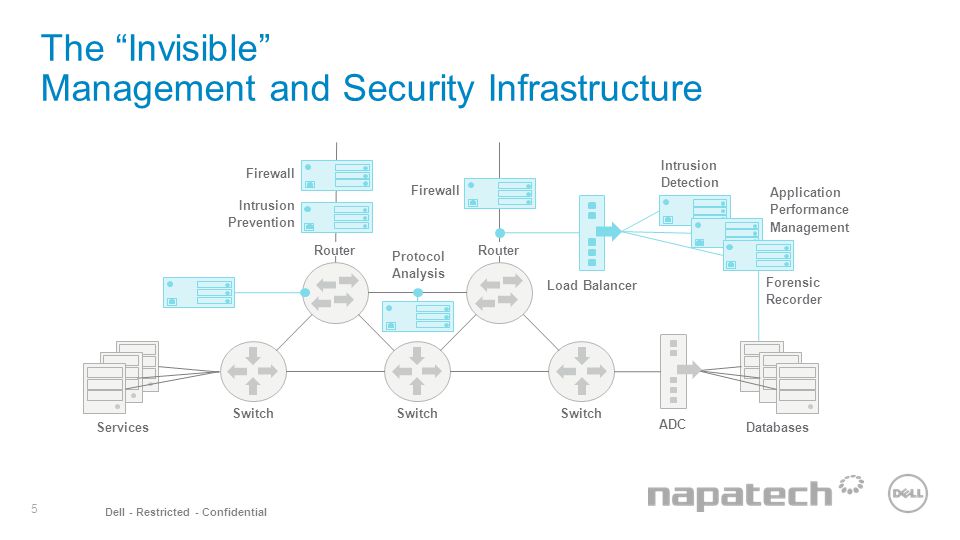
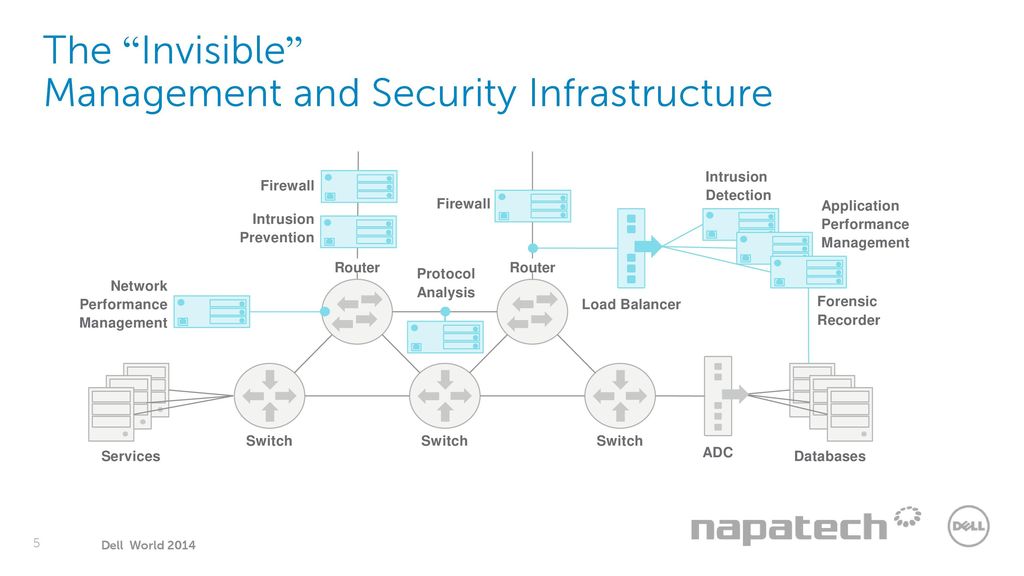
Napatech Acceleration Platform Powered by Dell. 2 Dell - Restricted - Confidential Accelerate Performance and Time-to-Market On October 21 st Napatech. - ppt download

![Tracking Malicious Software Movement With An Event Graph Ladnai; Beata ; et al. [Sophos Limited] Tracking Malicious Software Movement With An Event Graph Ladnai; Beata ; et al. [Sophos Limited]](https://uspto.report/patent/app/20210012005/US20210012005A1-20210114-D00000.png)