System hacked alert after cyber attack on computer network. compromised information concept. internet virus cyber security and cybercrime. Stock-Foto | Adobe Stock

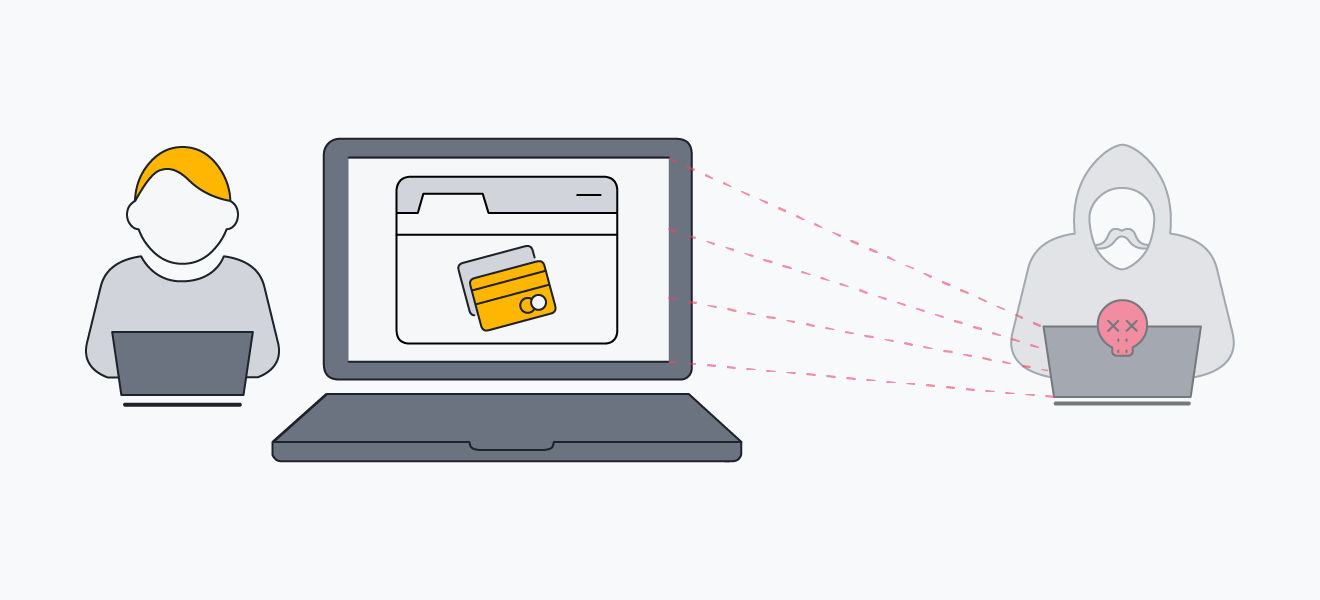
Compromised Computer Stock Illustrations – 203 Compromised Computer Stock Illustrations, Vectors & Clipart - Dreamstime

Laptop is hacked. Red attention sign on the computer screen. The concept of virus, piracy, hacking and security. Blue gradient background. Poster. Vector illustration 7473497 Vector Art at Vecteezy








.jpeg)